Why ZTNA
Zero Trust Network Access (ZTNA) is a modern security framework based on the principle of “never trust, always verify.” It ensures that users, devices, and applications are continuously authenticated and authorized before being granted access to resources—regardless of whether they are inside or outside the network.
ZTNA Enquiry Form


Access is granted based on verified user identity rather than network location.
This ensures only authenticated and authorized users can access applications.

Users are given access only to the resources necessary for their role.
This minimizes risk by preventing unnecessary or excessive access.

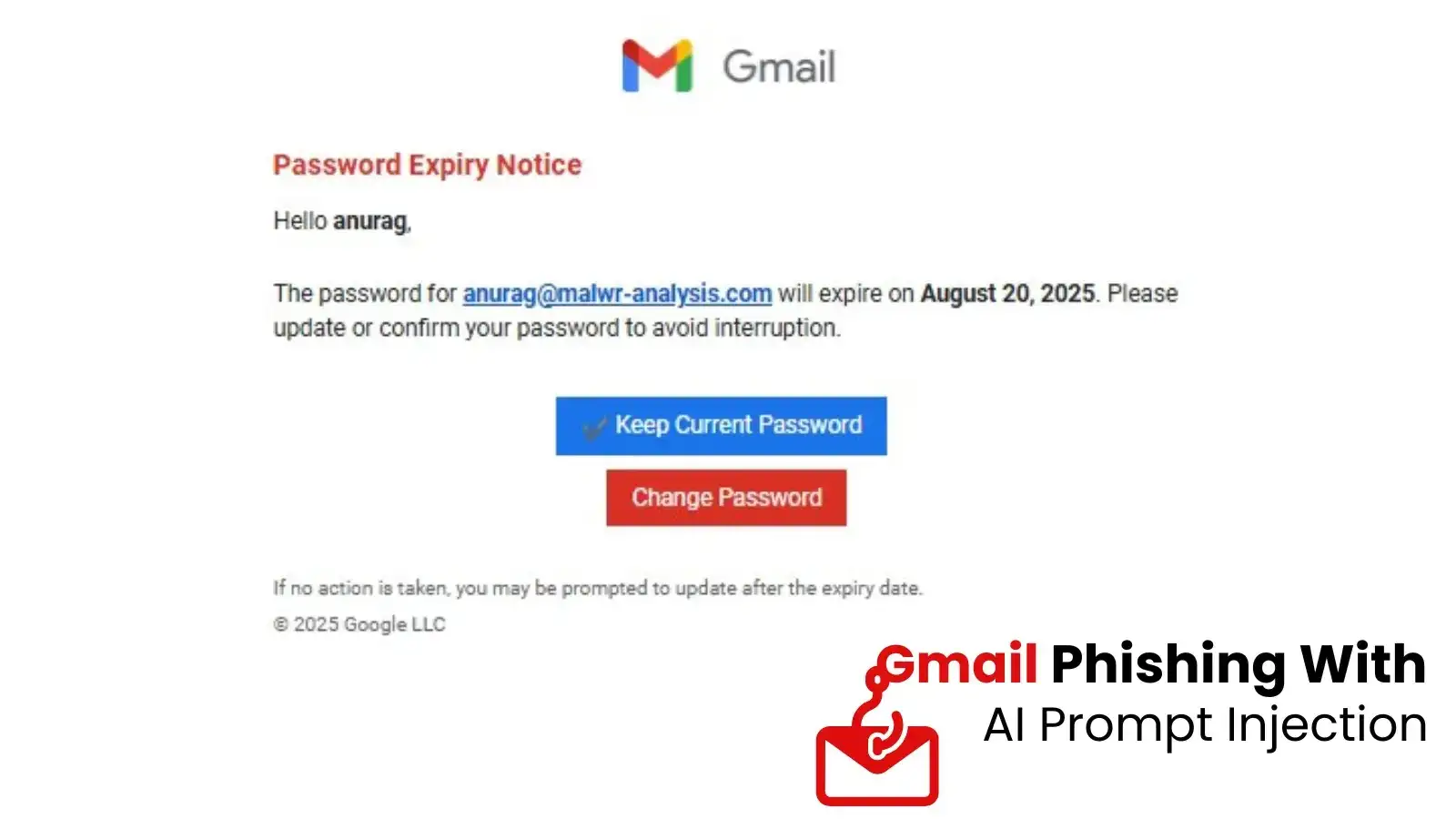
Adds an additional layer of security beyond passwords, such as OTP or biometrics.
It significantly reduces the chances of unauthorized access.

ZTNA verifies the security status of devices before granting access.
Only compliant and secure devices are allowed to connect to applications.

Access is restricted to specific applications instead of the entire network.
This reduces the attack surface and prevents lateral movement within systems.

User activity and access are continuously monitored in real time.
Any suspicious behavior triggers re-authentication or access restrictions.