Vulnerability Assessment and Penetration Testing
VAPT Services by Aquacodes ensure comprehensive cybersecurity through Vulnerability Assessment and Penetration Testing. We identify security weaknesses, simulate cyber-attacks, provide detailed reports, recommend remediation, and help protect your digital assets from threats. Stay secure, compliant, and resilient with our expert VAPT solutions.
VAPT Enquiry Form


Identifies weaknesses in internal and external network infrastructure such as open ports, misconfigurations, outdated firmware, and insecure protocols. It helps organizations understand their attack surface and prioritize remediation efforts to prevent unauthorized access, data breaches, and lateral movement across network environments.

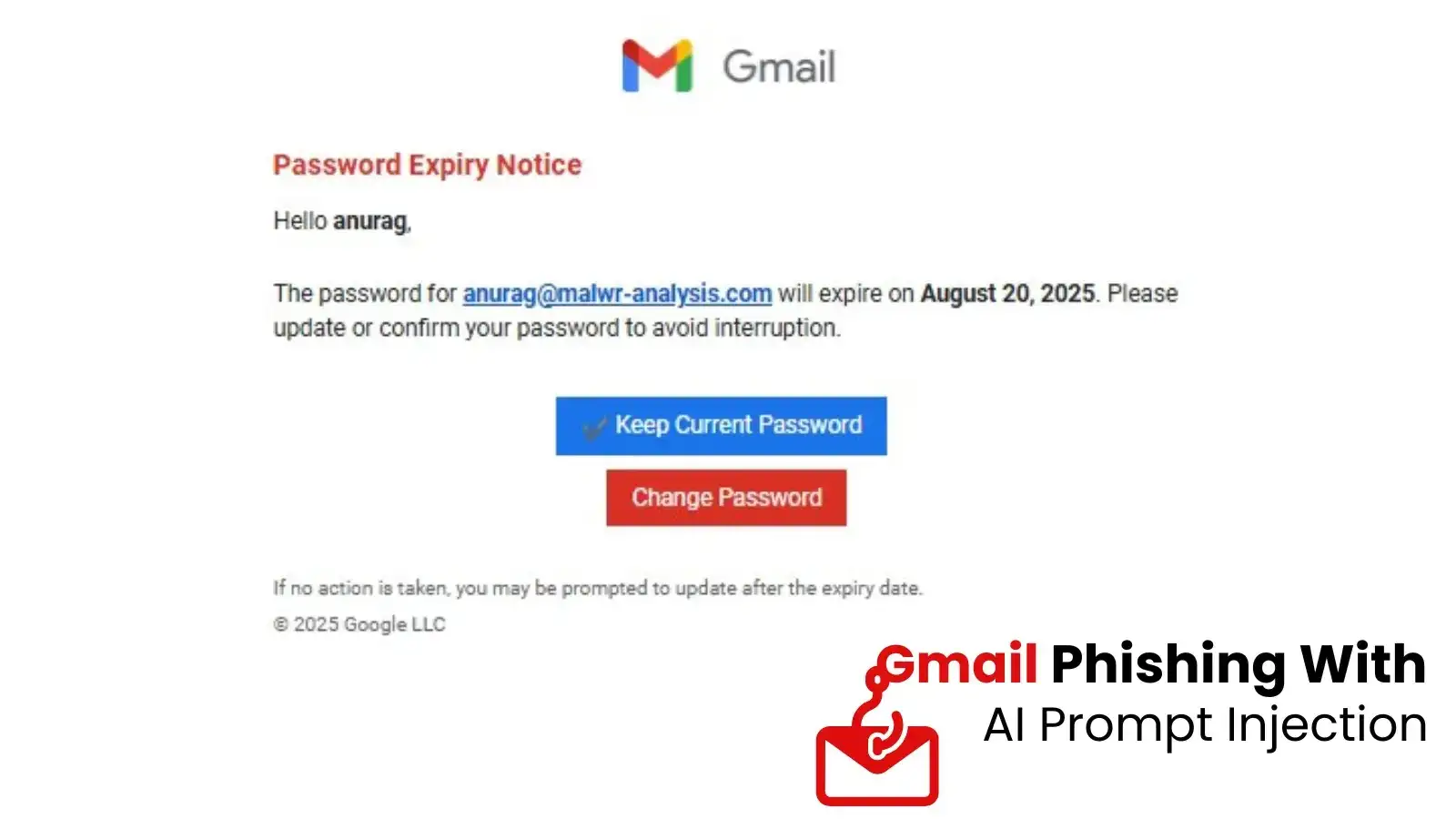
Simulates real-world attacks on web applications to uncover vulnerabilities like SQL injection, XSS, CSRF, authentication flaws, and insecure APIs. This service ensures applications are resilient against exploitation and aligned with security standards like OWASP Top 10.

Assesses Android and iOS applications for security flaws including insecure data storage, weak encryption, reverse engineering risks, and API vulnerabilities. It ensures mobile apps protect user data and resist attacks from malicious actors in real-world usage scenarios.

Evaluates APIs for vulnerabilities such as broken authentication, data exposure, rate limiting issues, and injection attacks. Since APIs are a major attack vector, this testing ensures secure communication between systems and prevents unauthorized data access or manipulation.

Reviews cloud environments (AWS, Azure, GCP) for misconfigurations, identity and access management issues, exposed storage, and insecure services. It ensures cloud infrastructure follows best practices and compliance standards while minimizing risks in shared responsibility models.

Analyzes Wi-Fi networks for vulnerabilities like weak encryption, rogue access points, poor segmentation, and unauthorized access risks. It helps secure corporate wireless environments against attacks such as eavesdropping, man-in-the-middle, and unauthorized network entry.

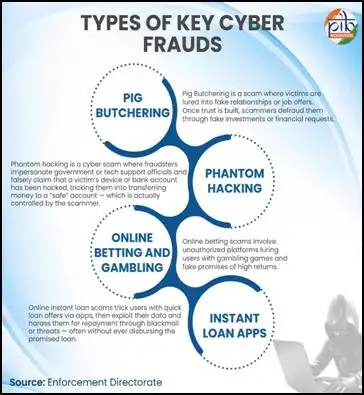
Simulates human-based attacks like phishing, vishing, and pretexting to evaluate employee awareness and response. This service identifies gaps in security culture and helps strengthen user training to reduce risks from one of the most common attack vectors.

Examines systems, servers, databases, and applications against security benchmarks (CIS, ISO, NIST). It ensures proper hardening, patching, and compliance alignment, reducing vulnerabilities caused by poor configurations and strengthening overall security posture.

A comprehensive, goal-based simulation of real-world cyberattacks targeting people, processes, and technology. It goes beyond standard testing to assess detection and response capabilities, helping organizations understand how well they can defend against sophisticated, persistent threats.